When I started blogging here about 18 months ago, I knew that I was having trouble identifying myself as exactly “libertarian”, despite that being my primary blogging perspective for years before that. I’ve mapped out important parts of this “new” position in previous posts, but now I think it would make sense to put everything in one place. This post is labeled “2.0” since former postlibertarian.com blogger Joshua Hedlund defined it pretty well in 2011. This is a more in depth analysis.
Continue reading What is Postlibertarianism? v2.0
Tag: encryption
Encrypted Communication Apps
I have discussed this idea in the past, but normally I’ve only gotten excitement about encrypted communication from my fellow libertarians and netsec friends. But with the current Presidential situation, there seems to be more interest in communicating without being overheard by the government, even among my government-loving left-wing friends. And this is excellent! Even if you don’t need privacy, by communicating securely all the time, you make it less notable when you do have to communicate securely, and you create more encrypted traffic that other government targets of surveillance can blend into.
First, let’s go over a very quick summary of encryption. If you’re already familiar with encryption, skip down past this section and the pictures to the list.
Public Key Encryption in 5 Minutes
An encryption algorithm takes information, like text, numbers, picture data (it’s all just 0s and 1s to computers) and outputs different text on the other side. A good encryption algorithm will output text that looks randomly generated so that no information can be gained about the source text. That output is then sent out in the clear (over the internet, where people might be spying) to the recipient. The recipient then reverses the process, decrypting the message and getting the original text, numbers, picture data, etc. However, if an algorithm always created the same output data from the same inputs, bad guys could figure out what you were saying pretty quickly. This introduces the idea of keys. A key is a number the algorithm uses to change the output in a predictable way. If both the sender and the recipient have a secret key, they can use their keys and the algorithm to send messages that only they can read (without the right key, the algorithm won’t reverse the encryption):

But we can do better! In our previous scenario, we need to somehow communicate the secret key separately from our message. That’s a problem, since we likely are using encryption precisely because we can’t communicate openly. The solution is something called public key encryption. In this system, each person has two keys, one public and one private. To send someone a message, you can encrypt the message with their public key, and then send it to them. Then only they alone can decrypt the message with their private key.

The reality of the mathematics is slightly more complicated, but for our purposes, what matters is how the public and private keys exist in each messaging app. Messing with these keys is difficult and confusing for users, but loss of the private key means communication is unsecured. Therefore, when using encrypted messaging, it’s important to be aware of how the app uses and manages the keys.
The Best Apps
The following is my ranked order of preferred secure communication:
1. Signal. This the gold standard encrypted communication app. It’s open source, free, has group chat, works on mobile and desktop, and of course is end-to-end encrypted. It even has encrypted voice calls. The one significant drawback is that it requires a phone number. It uses your phone number to distribute your public key to everyone that needs to contact you. Because of this, it offers excellent encryption (requiring no security knowledge!), but no anonymity. If you want that, check the next entry.
2. PGP Encrypted email. So this one is a bit complicated. OpenPGP (stands for Pretty Good Privacy) is an open protocol for sending encrypted messages. Unlike the other apps on this list, PGP isn’t an app and therefore requires you to produce and manage your own keys. The tools you can find at the link will allow you to produce a private and public key pair. To send a message to someone else, you will have to obtain that person’s public key from them, use the software to encrypt the message with their public key, and then send it to them. Because it is so much work, I have this method second on the list, but there is no better way to communicate securely and anonymously. To better distribute your public key, I recommend keybase.io (use that link to send use encrypted emails!). The good thing about PGP is that it can be used with any email, or really any other method of insecure communication. Additionally, it’s open source, free, and very encrypted.
Both Signal and PGP are very secure methods of communication. The following apps are good, but they are not open source and thus are not as provably secure. They are still better than just using unencrypted methods like SMS text, email, etc.
3. Whatsapp. WhatsApp is pretty good. It’s free, widely used, implements Signal protocol (and requires a phone number), works on mobile and desktop, has group chat and encrypted phone calls, and is encrypted by default. Moxie Marlinspike, the guy who made Signal, the number one app on this list, actually implemented the same Signal protocol on WhatsApp. That’s great, but unfortunately, WhatsApp isn’t open source, so while Moxie vouches for WhatsApp now, we don’t know what could happen in the future. WhatsApp could push out an update that does sneaky, but bad things, like turning off defaults. It’s also important to acknowledge that WhatsApp’s implementation already isn’t perfect, but it’s not broken. If you use WhatsApp, it’s important to make sure the notifications are turned on for key changes. Otherwise, it’s an excellent, widely used texting substitute.
4. Threema. Threema has an advantage in that it isn’t based in U.S., and it’s more security focused than Whatsapp. Threema is fairly feature rich, including group chat, but it isn’t free, it’s limited to mobile, and it isn’t open source. Threema uses the open source library NaCl, and they have a validation procedure which provides some comfort, although I haven’t looked at it in depth and can’t tell if it proves the cryptography was done perfectly. This paper seems to indicate that there’s nothing obviously wrong with their implementation. Nonetheless, it cannot be higher on this list while still being closed source.
5. FB Messenger secret conversations. Facebook Messenger is a free app and when using its secret conversations options, the Signal protocol is used. The app is also widely used but it takes effort to switch the conversations to secret. An encrypted app that isn’t encrypted by default doesn’t do much good. FB Messenger does let you look at your keys, but it isn’t as easy to check as it is in WhatsApp, and since it isn’t open source, keys could be managed wrong or defaults changed without us knowing. It also doesn’t have other features like group chat or desktop versions.
6. iMessage. Apple has done a good job with an excellent secure protocol for iMessage. It’s also feature rich, with group chat and more, but it’s only “free” if you are willing to shell out for Apple products. While Apple does a good job documenting their protocols, iMessage is not open source, which means we can’t verify how the protocol was implemented. Moreover, we cannot view our own keys on the app, so we don’t know if they change, and we don’t know how Apple manages those keys. It is therefore possible that Apple could either loop government spying into their system (by encrypting all messages with an extra master key) or simply turn over specific keys to the government. The amount you are willing to use iMessage to communicate securely should be determined by the amount you trust Apple can withstand government attempts to access their security system, both legal and technological.
Things I have specifically not listed on purpose:
- Don’t use SMS. It’s not encrypted and insecure. It would be good to not even use it for 2-factor authentication if you have a better option.
- Don’t use email. It’s not encrypted and insecure.
- Don’t use Telegram. They created their own “homemade” crypto library which you should NEVER EVER DO. Their protocol is insecure and their encryption is not on by default. In fact, there are at least two known vulnerabilities.
Leave a comment on the official Reddit thread.
Links 2017-1-12
As we approach the time when free trade is the heretical advice rather than the obvious logical one, it’s time to brush up on our free trade arguments. Here’s an interesting one: would you ban new technology to save the jobs tied to the technology it replaces? Would you ban light bulbs to save candlemakers? Cars to save horsebreeders? It’s a ridiculous proposition to freeze the economy at a certain point in time. Well, there’s no economic difference between new technology and free trade. In fact, we can treat international trade as a fancy machine where we send corn away on a boat and the machine turns the corn into cars.
And speaking of free trade, this is the economic modeling for why a tariff is unequivocally inefficient. One of the impacts of a tariff, by the way, is an increase in the market price of a good. Anyone saying that a tariff won’t have negative effects on consumers is just plain wrong.
The excellent open source encrypted messaging app Signal is so useful, it has to avoid having its application servers blacklisted by oppressive regimes. It uses a workaround of having encrypted connections through content delivery network, in this case, Google itself. Moxie Marlinspike, the creater of Signal says “Eventually disabling Signal starts to resemble disabling the internet.”
One of the biggest problems with Trump I pointed out last year was the total unknown of his policies. He keeps changing his mind on almost every issue, and when he does speak, he wanders aimlessly, using simplified language that is more blunt and less precise. Fitting right into this pattern, Trump has taken to Twitter for much of his communication, even since winning the election. Twitter is a short and imprecise tool for communication, and this New York Times article shows just how much uncertainty Trump creates with his tweets.
Related: Bill Perry is terrified of increased nuclear proliferation. The article is a little alarmist, but it’s worth remembering that nuclear war was a real threat just 30 years ago. It should not be taken for granted that nuclear war will never occur, and Trump seems the most likely of the post-Soviet presidents to get involved in a confrontation with a major nuclear power.
Scott Alexander reveals his ideal cabinet (and top advisers) if he were president. It’s not only remarkably better than Trump’s, it’s probably better than any cabinet and appointees we’ve ever had (Bernie Sanders notwithstanding). Highlights include: Alex Tabarrok as head of the FDA, Scott Sumner as Chairman of the Fed, Charles Murray as welfar czar, Peter Thiel as Commerce Secretary, and Elon Musk as both Secretary of Transportation and Energy.
Speaking of cabinets, George Will details just how out of touch soon-to-be-Attorney General Jeff Sessions is, recounting his 2015 defense of unlimited civil asset forfeiture, a procedure by which the government takes cash and property from civilians who have been convicted of no crime and therefore have no recourse or due process protections. Don’t buy into the story that all of Trump’s appointees are horrific and terrifying; there is a gradient of his cabinet appointments depending on their authoritarian tendencies and the importance of their department, and unfortunately Jeff Sessions as Attorney General is by far the most concerning.
Missed this earlier last year, and worth keeping in mind as BuzzFeed gets hammered this week over their publishing of an unverified dossier: apparently the FBI already has daily aerial surveillance flights over American cities. These seem to be for general investigative use, not vital national security issues: “But most of these government planes took the weekends off. The BuzzFeed News analysis found that surveillance flight time dropped more than 70% on Saturdays, Sundays, and federal holidays.”
Speaking of BuzzFeed and the crisis of “fake news”, which itself may not even be anything compared the crisis of facts and truth itself, Nathan Robinson has an excellent take on the matter (very long read). With the lack of facts in the election, the media and Trump’s critics generally have to be twice as careful to rebuild trust in the very concept that objective truth exists and can be discussed in a political context.
Government regulations have hidden, unexpected costs. These regulations hurt people regardless of their political affiliations, as a Berkeley professor found out when trying to evict a tenant that refused to pay rent. California’s rather insane tenant laws mean that serial rent-cheaters can go from place to place staying rent free for months at a time.
I’ve often thought about the right ordering of presidents from best to worst, taking into account a libertarian, liberty-promoting approach. One difficulty is the non-comparability of presidents separated by centuries. However, this blog post from 2009 actually does a nice job of scoring the presidencies. I don’t agree with each one, but it’s a rough categorization that makes sense. It even gave me an additional appreciation for Ulysses Grant, who I figured was mostly president by the luck of being the general in charge when his army won the Civil War. Other highlights include William Henry Harrison scoring 11th, thus beating over three quarters of the competition despite only being in office for a month. I feel like I could have found more worse things on Andrew Jackson, and in general I feel like I agreed with the list more the closer I got the end.
Jeffrey Tucker at FEE has a nice article about the difference between spreading ideas and actual economic production of goods. His thesis is that we have much less control over the developing of ideas than we do of developing normal rivalrous goods. And since libertarians are pretty solid at grasping the idea that the production of goods cannot be controlled from the top down, we should also acknowledge that top-down approaches to developing ideas are even more preposterous, especially in the digital age of decentralized information. I’ve thought about this a fair amount considering I like I blogging but I’m well aware few people read this blog. The simplest way to restate Tucker’s point is that you have to have good ideas more than good distribution. I don’t know if that’s an accurate take, but certainly good ideas are the single most important part of spreading your ideas.
There’s a saying on the internet that “Democracy is two wolves and a lamb voting on what to eat for lunch”. The 2016 election is excellent demonstration of just how poorly democracy can fail, but what our all alternatives. How about Futarchy? This is Robin Hanson’s idea to improve public policy: “In futarchy, democracy would continue to say what we want, but betting markets would now say how to get it. That is, elected representatives would formally define and manage an after-the-fact measurement of national welfare, while market speculators would say which policies they expect to raise national welfare.” Let’s hold a referendum on it; those seem to work out.
Bitcoin has been on the rise in recent months. So have other cryptocurrencies. But rather than focus just the price of the cryptocurrency, why not look at the total market valuation of those currencies? Sure, you might have heard that Bitcoin was up to $1000 again recently, but did you know that its total market cap is ~$13 billion? At the very peak of the Bitcoin bubble in 2013, all Bitcoins together were valued around $13 billion, but only for a matter of days. This time Bitcoin has kept that valuation for over 3 weeks. With more markets and availability, Bitcoin is becoming a real alternative for people whose national currencies have failed them.
Postlibertarian throwback: When Capitalism and the Internet Make Food Better. A reminder that the despite the ongoing horrors of government we are witnessing, the market is still busy providing better products and cheaper prices.
Model-Breaking Observations in the Senate
It’s rare when an idea, or piece of evidence, comes along that is so impressive, it forces you to rethink your entire model of the world. The recently released Feinstein-Burr encryption bill has done just that.
It has been described as “technically illiterate”, “chilling”, “ridiculous”, “scary”, and “dangerous“. Not only are the issues with the bill fairly obvious to anyone with a cursory understanding of encryption, the problems are of such magnitude that it thwarts any attempt to understand the Senators’ actions. Let’s look at the effects of the hypothetical law.
The biggest issue is that this bill will significantly damage the United States’ national security. We live in a highly insecure world where cyberattacks, both foreign and domestic, are omnipresent. The Feinstein-Burr bill would fundamentally reduce the security of all technology infrastructure in the country. Jonathan Zdziarski in a blog linked above, gives some details:
Due to the backdooring of encryption that this legislation implies, American electronics will be dangerously unsafe compared to foreign versions of the same product. Diplomats, CEOs, scientists, researchers, politicians, and government employees are just a few of the people whose data will be targeted by foreign governments and hackers both while traveling, but also whenever they’re connected to a network.
That’s awful, and even if you have the most America-first, protect-American-lives mentality, weakening American encryption is the worst thing you could do; it literally endangers American lives.
I think there’s also a strong case to be made that this will do very little to combat terrorism. Unbreakable, strong encryption is widely available on the internet for free, forever; if bad people want to use it, they will. Moreover, terrorism, as awful as it is, is relatively rare; Americans are about a 1000x more likely to die non-terrorism related homicide. And many more “common” homicides occur due to heat-of-the-moment arguments, which means there would be no encrypted messages detailing conspiracies. All this bill does is remove the ability of average, non-technically inclined Americans to secure their data.
And the people whose data will be most at risk will be those consumers who are less educated or less technically adept. Better informed consumers might have the ability to install foreign encryption software on their phone to keep their data safe, but most uninformed consumers just use default settings. Thus, criminals who try and commit identity theft will greatly benefit from this legislation; they wouldn’t usually bother targeting knowledgeable users anyway, and with security stripped away from phones, it will be much easier to steal data from susceptible users. The people most in need of help to protect their data will be disproportionately harmed by this legislation.
On the other hand, most companies are not uniformed users. They have IT departments who understand the value of encrypting their data, and they will continue to purchase strong security software, even if it is no longer sold in the United States. Foreign produced software works just as well. Banning strong encryption will debilitate the American technology sector, one of the biggest and most important parts of the economy. This will cost Americans jobs and diminish America’s influence on the future of the world, as technological innovation moves overseas. But this isn’t just bad for Americans; it’s not easy to simply move an entire company or product overseas. There are huge capital investments these companies have made that will not be available in other countries immediately, if ever, and this will set back the global technology industry billions if not trillions of dollars.
So this really begs the question of why Senators Dianne Feinstein and Richard Burr introduced this bill; given their stated obsession with national security, and given the horrific effect this bill would have on American national security, there’s no good way to resolve their stated beliefs with their actions. Here are a couple theories to explain their behavior, and some discussion as to why each respective theory is unsatisfying.
The Senators are actually foreign spies purposefully trying to weaken American national security. Obviously, if this theory is true, it’s self-evidently very bad that our elected officials not only don’t represent us, but actually represent foreign governments likely trying to harm Americans. Sure it’s quite unlikely since it’s very difficult to become a U.S. Senator at all, and no spy agency would send agents in with a plan to become a U.S. Senator. Whether they were turned into foreign agents after being elected, I really can only speculate. But it strikes me as improbable. Nonetheless, it is true that this legislation is exactly what foreign security agencies would want to introduce to make the United States more vulnerable. I was curious, so I checked the constitutional definition of treason as well as the Espionage Act, but it seems that you need to literally give secrets to other people, not just make it easier for them to obtain. But there is that one case where a high ranking official is in trouble for storing documents insecurely…
They’re power hungry politicians. The idea of the Senators being foreign spies is bit far-fetched. But what know for sure is that they are politicians, which means they chose a career path that would give them more power to change things. Maybe Burr and Feinstein are sick of technology companies telling the FBI that they can’t assist their investigations, and they wanted to put them in their place. If this theory is true, it’s pretty self-evidently evil; people in power using their power indiscriminately to harm citizens is the exact problem Thomas Jefferson identified in the Declaration of Independence. Of course, it’s not usually a big problem, because James Madison helped construct a whole host of ways to check the power of government. Of course, the most important check for our situation is that senators are voted in by the people. So as long as people know about this dumb bill, they’ll kick these guys out…right?
Hanlon’s Razor (origin disputed) states that one should “never attribute to malice that which is adequately explained by stupidity.” This theory would mean that two sitting, highly experienced U.S. Senators are too stupid to realize the ill effects this will have on national and economic security. Obviously, congress has to make laws in areas that its members are not always familiar with…but Burr and Feinstein are the chair and vice chair, respectively, of the Intelligence Committee. If anyone knows about intelligence, they do. And Feinstein is even on the Judiciary Subcomittee on Technology, Privacy, and the Law! If even these people are too stupid to understand what the effects of their own policies are, we might as well stop sending representatives to a legislature at all and just have run-of-the-mill uneducated voters pass everything directly through referendum. Sure, they’d have no idea what they’re doing, but apparently neither do Senators!
What I think is most likely, and most terrifying, is that American Democracy incentivizes members of Congress to make bad policy if it’s politically beneficial. With all the aides and staff Senators have, plus the amount of pressure they receive from outside groups, it seems unlikely they never heard about the bad effects of the bill. Yet, they did it anyway. Given they don’t work for law enforcement, there is no Frank Underwood endgame for passing this bill; banning encryption doesn’t directly allow Burr and Feinstein to look at their political enemies’ phones (…probably), just criminals and the police. So then maybe their incentive was to appear tough on crime and terrorism, consequences be damned. Richard Burr is in a reelection year in North Carolina, so let’s look at the effect this horrible bill has had on his chances to win according to Predictit.org:
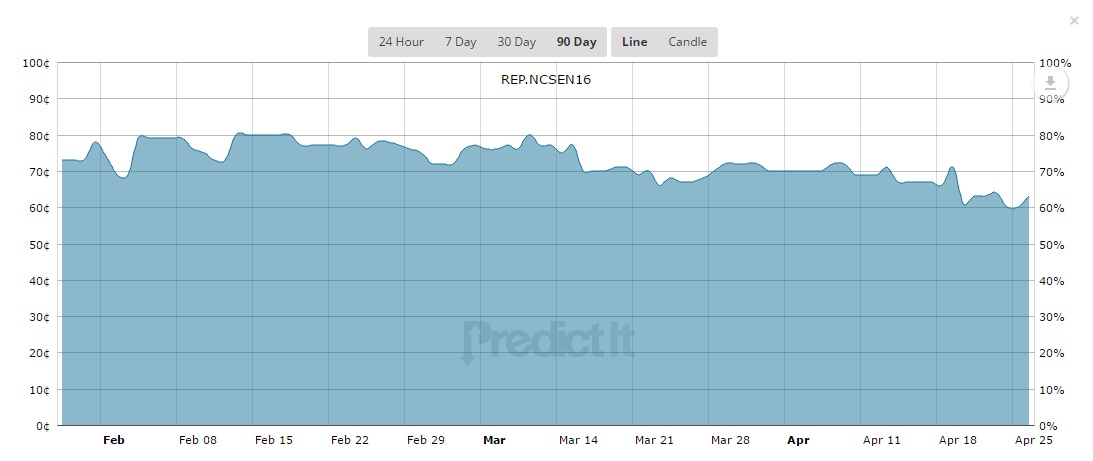
As you can see, the bill had very little effect on his perceived chances. Now, it could be that voters have already factored in Senator Burr’s position on destroying defending American national security, and he needed to introduce this legislation to maintain his position. But it looks identical to a situation where North Carolina voters couldn’t care less about Senator Burr’s position on encryption, and his introduction of legislation consequently had no effect on his reelection chances. If it’s the former, then we are in serious trouble because our legislative representatives are incentivized to make horrible policies because voters aren’t well informed. If it’s the latter, then we have to dismiss this explanation and go back to one of the other three.
Whatever the explanation is, it reflects poorly on how the government constructs policy, and it reflects poorly on American Democracy. Moreover, assuming any of those discussed theories are true, they imply massive issues that will be difficult or impossible to solve. Reforming democracy as many progressives would like, through campaign finance, wouldn’t even address any of these issues; it is the technology corporations and privacy NGOs which have been advocating for more privacy and making unbreakable encryption more accessible, while law enforcement and other government agencies have been advocating for less security. But as far as I can tell, even they haven’t demanded anything like this bill. Thus, more campaign spending by private groups would help, not hinder good policy.
No matter how you look at it, this bill indicates a big failure for democratic government and illustrates the dangers discretionary state power.
Photo credit: Caïn venant de tuer son frère Abel, by Henry Vidal in Tuileries Garden in Paris, France, photo by Alex E. Proimos, licensed under CC-BY-2.0.
Legal Innovation: Warrant Canaries
I recently came across a fascinating legal concept called warrant canaries. I’m going to cover the idea briefly, but if you want to know more about them in detail, I highly recommend this Warrant Canary FAQ at the Electronic Frontier Foundation.
The context is that many online services based in the United States can be compelled by the FBI to give whatever information they have to law enforcement through National Security Letters. Those documents often gag the companies from informing their customers they are being spied on, even if the service is being provided specifically so that users can get encrypted, private communication. It’s hard to pin down the exact constitutionality of NSLs. They were ruled unconstitutional in 2013, but it looks like the case was remanded in 2015 after the passage of the USA Freedom Act. Given the government’s continued efforts to obtain information regardless of constitutionality and limitations placed on them by Congress, it would be nice if we had some way to communicate if a service was under duress from the government.
The usefulness of warrant canaries (I’ll get to what they are in a moment) is based on two legal concepts: (1) it’s not illegal to inform anyone of a warrant you haven’t been served, and (2) the state cannot compel false speech.
The first statement is common sense, since you can’t be curtailed from simply stating something hasn’t happened yet. The second is a bit more subtle; a stronger statement is that the state cannot compel speech at all, but that’s not always true. The state can sometimes compel commercial speech to inform consumers of information so they can make accurate decisions. The EFF elaborates that “…the cases on compelled speech have tended to rely on truth as a minimum requirement”.
This is essential because it allows companies with encryption products to convey highly relevant information to their customers. Companies can publicly post a message indicating they have not received a warrant because of the first legal concept, and they can immediately take down their public message when they do receive a warrant because the state cannot compel false speech.
To ensure the authenticity of the message stating that the given company has not been subject to a NSL, many go an extra step and sign their messages with a PGP key (example here).
Of course, a foolproof way to ensure no data is lost is to simply make all data encrypted, like Apple has with the iPhone, ProtonMail does for email, and everyone who has ever sent encrypted emails has been doing since the 90s. But I still like this idea, because individuals who run encryption services should not be forced to be government puppets, like the FBI hoped to do to Ledar Levison.
The weakness is that we don’t know what we don’t know, so it’s possible the government already has a new Secret National Security Letter which it uses to compel companies to lie under some made up interpretation of an arcane piece of legislation. The only real security is end-to-end encrypted communication or being Hillary Clinton.
Banning Unbreakable Smartphone Encryption is Stupid
At least two states, New York and California, have introduced legislation that would ban smartphones sold in those states if those smartphones could not be searched under request from law enforcement. This would likely mean no phones would be sold with unbreakable encryption, although I suppose Apple or Samsung could manufacture two types of phones and then just sell all the encrypted ones from New Hampshire or something. These bills are still somewhat controversial, and as it has gotten press coverage, there has been a House bill introduced that would prevent state legislation like those bills introduced in New York and California. Continue reading Banning Unbreakable Smartphone Encryption is Stupid
Links 20160224
Marginal Revolution has a post about an event that occurred on Shark Tank. The pitch on the show was an alternative to bee honey, made from apples. Part of the pitch was that this would save the bee population by reducing the industrial demand for it (yes, really). Spoiler from Professor Tabarrok: “Reducing the demand for honey, reduces the demand for bees”.
Politico has a nice article about the potential of Bernie Sanders’ campaign, even if he doesn’t win a majority of delegates. The way the Democrats set things up, he will be in an excellent position to make demands on the party platform, possibly reshaping the Democrats’ economic policy for many years to come.
A recent Quinnipiac poll found that head-to-head, Sanders beats Trump by 10 points in a national survey (he does better than Clinton against Trump). Things could change of course, but it seems that Trump really isn’t who I should be worried about becoming president right now, as he’s still not likely to win the Republican nomination, and it seems the Democrats poll well against him.
SCOTUSblog has a nice write up on the next court nomination fight, now that Scalia is gone, what factors will be in play, and how can the Obama administration find a nominee with a spotless record that fires up the base and ensures a left-of-center court for a long time. I doubt they nominate a classical liberal.
Tyler Cowen writes about the benefits market monetary policy can bring, as well as the shortfalls of its approach when critiquing Fed policy.
Apple CEO Tim Cook posted a public letter to Apple customers detailing a demand made by the FBI. Law enforcement wants the company to create a new version of their operating system which they could then install on a criminal’s seized phone. The new OS would have a backdoor allowing the FBI to more quickly access it. I liked Apple just fine as a company, but this is pretty awesome. This week, it turns out the FBI was lying about this being a one-time request as the DoJ is already pursuing orders to force Apple to unlock about a dozen other phones, according to anonymous sources.
Nostalgia Critic on Channel Awesome on YouTube has a great video detailing the absolutely horrible copyright abuse rampant on YouTube. Claimants have no repercussions for false claims, even on self-evident fair use cases because YouTube’s system is entirely automated with no oversight. Copyright battles are not something of the past, there are still huge problems today.
An NBER study from last year found government subsidies more than account for increases in tuition. H/t Slate Star Codex.
The German government gives us another example of how you can’t have government surveillance without fundamentally breaking security. Hacker News discussion.
Second link from Alex Tabarrok, this time on drug prices and the FDA. Apparently the US has the lowest generic drug prices of any developed nation. I feel like we should switch to a prize system where drug companies are awarded $X million for successfully passing approval, and then that drug is immediately released with no patent into the market. X could be set based on the amount of patients in the previous 5 years who could have used the drug.
People like to talk about the “Uber” of some industry, trying to say a company is disrupting their space like Uber did to taxis (also in the interest of fighting monopolies, Lyft is great too). How about Uber for welfare? The left often opposes “workfare”, or ways which incentivize welfare recipients to work, since finding jobs for everyone isn’t practical “…but today the gig economy offers the solution: It can easily and quickly put millions of people back to work, allowing almost anyone to find a job with hours that are flexible with virtual locations anywhere.” There’s also some data that working is a really good on a cultural level, teaching discipline and responsibility. This sort of goes against my attraction to a basic income, but could go hand in hand: you get a basic income allowance if you can prove you engaged in the gig economy recently. Really cool idea.
From EconLog, some praise for the Free State Project. Apparently they’ve already got over a dozen people elected to the state legislature? Tried to find somewhere else this is being tracked, but I didn’t see anything. If you have info on this, tweet at me.
Also from EconLog, Bryan Caplan finished his summarized his extended discussion of ancestry and long run growth literature. In sum, we can’t say that people with more advanced culture thousands of years ago had that much better outcomes today. It’s likely other institutional decisions are more important (like having stable free markets).
You must be logged in to post a comment.